Increase your resiliency against account takeover
Why are all accounts potential scamming targets? What can you do to protect yourself? Here are some actionable recommendations to make your accounts less attractive for most types of scams.
Guest contribution by Dario Salice, Identity & Security Expert

The Internet is a place to communicate, share, and conduct business. Some people’s businesses require them to gain access to other people’s accounts so they can then run their scams. These scams can range from faking ads clicks, spreading misinformation, asking for ransom, or conducting fraudulent e-commerce activity.
Not all targets are equally valuable
Not everyone’s account offers the same prospect of financial return for these bad actors. The ecosystem of this part of the criminal economy is as diverse as that of the “good economy”. Some of the scammers require access to large numbers of accounts to conduct their low-margin businesses, while others are going for “high-value” targets, where they expect a higher return on their investment.
(The following graph is meant to display the concept and does not reflect actual numbers or ratios across these cohorts.)
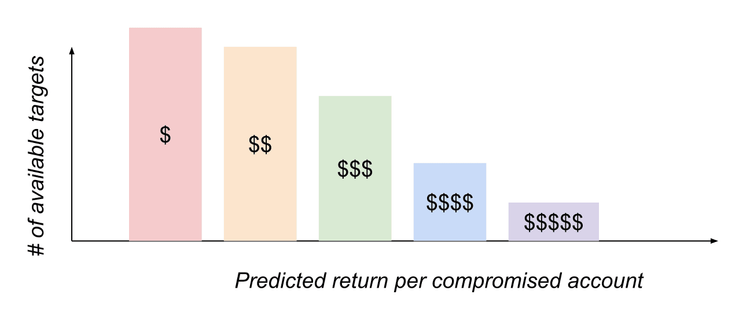
Taking the mental model that not all targets are equal and not all attackers are after the same victims, the scammers find their preferred segment, based on the scam they’re planning to run and the resources they can put into their attacks.
Using market intelligence data collection methods, these attackers then try to find the targets that can be compromised with as little effort as possible to maximize their margins.
Cost of compromise varies
Just as not all targets are equally valuable, the cost of compromising them varies highly depending on a couple of aspects:
Platform / Service: Not all accounts have the same level of built-in security. A general rule of thumb that a larger platform is safer than a smaller one, and regulated businesses like banks are obliged to make more investments to protect their customers is very simplistic but probably not completely wrong.
Your individual account security hygiene: Most account systems offer some levels of customizations, which you can use to increase the security baseline of your individual account. This is the part I am focusing on in this note, as it is in your power and interest to make compromising your account uneconomical.
The old phishing method is still good enough (for most)
If you thought that “only n00bs get phished, then I have disappointing news for you. Phishing is a type of attack that has been around for decades. The first known “modern” phishing attack is reported to have taken place in the 1990s, when bad actors tricked their victims to give them their AOL (America Online) passwords, after sending them malicious links via messenger.
While the attack methods have a bad reputation, many people overestimate their ability to spot phishing attacks; they are still a powerful tool. Whenever Security specialists think that they can tell people to look for spelling mistakes or old logos to detect phishing attacks, it gives me the shivers. If your defense strategy is based on the attacker’s inability or lazyness to spell correctly, you’re treading on thin ice.
Ready in about an hour
One example of how easy and powerful phishing can be is a free tool called evilginx2. With the help of this tool, and dozens of tutorials on the web, you can easily build your own phishing site in less than an hour. All you need is a cloud-service like Digital Ocean and a domain.
Setup is easy:
- Install the evilgix package on your linux installation.
- Register a domain and make some changes on your domain name server.
- Choose one of the services you want to impersonate. Templates for popular services like Twitter, Instagram, Microsoft, etc. are pre-installed.
- Create and share a link through which your victim will land on the fake login page.
What will happen then is almost magic. Once the attacker tricks their victim to click on the link, they will go through a login-flow that is indistinguishable from the real flow. Instead of providing their credentials to the correct website, they will send it to the fake website, controlled by the bad actor, that then will use it in realtime to login onto the correct site. Since this happens in real time, this will also work around most 2-Factor-Authentication methods - FIDO Security Keys are the only methods it won’t bypass - and provide the bad actor with access to your account.
EvilGinx2 acts as a proxy between the victim and the service they want to sign in to.
Ways to make your account more resilient against attacks
As mentioned above, this article focuses on what you can do to increase the resilience of your online accounts. None of these recommendations are meant as a silver bullet, but each one of them is an actionable recommendation to make it less economically attractive for most types of scams.
Step 1) Password hygiene
Make sure your passwords are unique and reasonably complex. Use a Password Manager to generate complex passwords and manage them in a safe place so you are less likely to lose them. Writing them down on a piece of paper is better (for most) than using predictable passwords like 1234, your phone number or something “smart” like “S3cur!ty”.
Step 2) Two-Factor Authentication (2FA)
Even the strongest password can be phished, so adding an additional layer of protection is an effective way to raise the Security Baseline of your account. While most platforms offer Two-Factor Authentication where you’re sent a short-lived and one-time use only code via SMS, some also offer alternatives that have different security characteristics. Generally speaking, the various methods offered by most platforms can be ordered by ranking their level of protection from (relatively) low to high:
Low:
- One-time code sent via email
- One-time code sent via SMS
Medium:
- Code generated via authenticator apps (e.g Google Authenticator, authy, etc.)
- Push notification with additional information about login attempts (e.g origin, device, etc.)
High:
- FIDO 2 Security Keys (see step 3)
Step 3) Use FIDO2 Security Keys where available
FIDO (Fast Identity Online) is a set of standards developed by the FIDO Alliance, an industry consortium with members like Google, Microsoft, Apple, Yubico, Visa and more. The current set of standards defining hardware security keys is called FIDO2.
FIDO2 certified Security Keys are a very secure way to perform authentication, and are supported on a growing number of platforms and services. Most services that support FIDO2 allow you to register your Security Keys as a 2nd factor method.
Some of the benefits of security keys compared to other 2FA-methods are:
- Authentication using FIDO Security Keys can’t be phished or intercepted by bad actors, because they ensure that the client is talking to the rightful server and not an impersonating phishing page.
- FIDO Authentication does not rely on a knowledge factor that can be stolen or guessed by an attacker.
- Using a FIDO2 Security Key protects you from sophisticated phishing attacks as the keys only work when used on the correct website or app.
While FIDO2 Security Keys are a great step forwards and deterministically thwart the most common types of attacks used for account takeover, they come with challenges and limitations.
- Cost of a FIDO Security Key can be up to CHF 50, depending on the vendor, type, and additional requirements
- Ensuring that everyone in the organization has a Security Key, and can get a replacement if lost, can be a logistical challenge
- Not all consumer and business tools support FIDO2 Security Keys. For businesses it’s sensible to connect as many of these tools to a centralized Identity Provider’s SSO (Single Sign-on) functionality and mandate Security Keys for all logins and, as well as for step-up authentication
While we’re not yet ready to completely move on from passwords, these suggestions are actionable steps to reduce our reliance on passwords.
Take action to prevent getting phished, it’s not that hard.
About the author
Dario Salice is a seasoned Product Manager and subject matter expert in the field of Identity & Security. Having worked at Google and Meta (Facebook) and been a Board Member at the FIDO Alliance, he was able to gain broad insights into this field. Currently he’s ramping up a boutique consulting business around Security and Product Management.

FAQ:
Q:What do I do If a service I use doesn’t support FIDO? A: Ideally you connect all your work-tools to your centralized Identity System using SSO. This way you benefit from the Security Baseline you have on your core-accounts. If SSO is not supported (in your tier) make sure any type of 2FA is enabled.
Q: Which service supports SSO, 2FA and FIDO? A: For 2FA support visit 2fa.directory and for a list with services that support FIDO, Yubico offers a comprehensive list. An overview of services that only offer SSO for higher tiers can be found on sso.tax.
How GObugfree will make it easier for you to protect your account
GObugfree takes the security of our customers and friendly hackers seriously. With the new release of the GObugfree platform, accounts can now be protected with Security Keys like Yubikeys - this as an extension of the previous 2FA using Authenticator apps. The Security Keys can be added in your user account. If possible, we recommend that this option be selected. If you have any questions, you can contact us at any time. GObugfree has also provided our employees with Security Keys to be used for both business and private accounts.