Bug bounty programs: A three-way view of cybersecurity in the financial sector
Each year, experts from financial institutions gather at the "Secure E-Banking" event to share insights. This year, the focus was on the rapidly growing trend of bug-bounty programs in Switzerland and Europe. Oliver Hirschi, initiator of "E-Banking - but safely!", recognized the importance of this topic and highlighted it at the event.

The annual "Secure E-Banking Symposium" at HSLU offered a special perspective this year: a threefold look at bug bounty programs. Three experts, Matthias Jauslin, Advisory Board Member at GObugfree & Managing Director of Enrol GmbH, Jens von der Haar, Head of Cyber Resilience & Response at Raiffeisen, and Mauro Mattia Sbicego, a long-time ethical hacker, guided the participants through the different facets of this emerging method in cybersecurity. Each of them shed light on the topic from their own unique perspective, creating a comprehensive understanding of the challenges and opportunities of bug bounty programs.
At the core of bug bounty programs: ethics and efficiency
Matthias Jauslin, GObugfree advisory member, clarified the misunderstood image of "hacking". While the public often sees hackers as villains, ethical hackers, or "bug bounty hunters", play a constructive role. In bug-bounty programs, these ethical hackers are tasked and authorized to find vulnerabilities in digital systems. They get rewarded based on the severity of the discovered flaw.
Bug bounty hunters play a critical role in protecting digital systems. Their ethical approach provides organizations with an additional layer of security. By continuously searching for security vulnerabilities from different angles, they ensure that systems are continuously audited and thus kept secure at all times. Matthias explained, "Bug bounty programs offer the most honest and clear view of actual information security with the highest ROI – you only pay for effectively found vulnerabilities."

Matthias Jauslin, Advisory board member at GObugfree
"Bug bounty programs offer the most honest and clear view of actual information security with the highest ROI – you only pay for effectively found vulnerabilities."
What drives ethical hackers
Matthias also shed light on what motivates ethical hackers. Many ethical hackers are driven by a deep passion for hacking and see it as a kind of puzzle they want to solve. However, there are other reasons that lead them down the ethical path: monetary incentives through rewards, a desire to protect businesses, ongoing education, a sense of community, and last but not least, the sheer fun of the challenge. He says, "This combination of factors makes ethical hacking an invaluable part of modern cybersecurity." GObugfree, the first Swiss vulnerability management platform with the swiss made software label, has made it its mission to promote this ethical approach. Through clear frameworks, motivating reward mechanisms and thorough validation processes, GObugfree ensures that both companies and hackers can benefit from this system.
Customer Perspective: Bug-Bounty Programs as Essential Security Tools
Jens von der Haar, with a background in pentesting and IT forensics and now at Raiffeisen, understands the importance of cybersecurity. For Raiffeisen, being proactive and constantly adapting is key. Jens sees pentests and bug-bounty programs as two pillars of a robust security strategy. He highlighted the high costs, both financially and reputationally, of cyberattacks on institutions like Raiffeisen.
The financial and reputational risks of cyber attacks
An attack by cybercriminals can be catastrophic for financial institutions like Raiffeisen. Jens points out, "Most successful attacks require hours or even days for detection and full recovery. Because bug bounty programs expose existing security vulnerabilities, they offer an unbeatable ROI." Beyond the direct recovery costs, the potential financial and reputational losses are immense. Although investments in security measures may initially seem high, they are a fraction of the cost of a single successful cyberattack. Bug bounty programs are thus a preventive measure that definitely pays off in the long run.

Jens von der Haar, Head of Cyber Resilliance & Response at Raiffeisen
“Most successful attacks require hours or even days for detection and full recovery. Because bug bounty programs expose existing security vulnerabilities, they offer an unbeatable ROI.”
Raiffeisen's gradual approach to bug bounty programs
Raiffeisen chose GObugfree as its trusted partner for its bug bounty program. The bank is taking a strategic and phased approach to implementation. Initially, Raiffeisen launched a private program with a select group of hackers coordinated by GObugfree. Security vulnerabilities were systematically forwarded to internal teams, with particular emphasis on effective communication and management. Over time and once internal processes were firmly in place, the scope was expanded to cover more applications. This approach ensures that developers and the security team are not overwhelmed and can grow together.

The benefits of the GObugfree bug bounty program for Raiffeisen
At Raiffeisen, the GObugfree bug bounty program has proven valuable and offers numerous benefits:
- Broader perspective: The diversity of ethical hackers involved gives Raiffeisen a more comprehensive overview of potential security vulnerabilities.
- Specialization of testers: Each tester has their own areas of expertise, resulting in more in-depth and specialized testing.
- Continuous testing: In contrast to time-limited pentests, the bug bounty program provides continuous monitoring.
- Rapid availability of testers: Qualified testers can be called in quickly when needed.
- Success-based compensation: Only vulnerabilities that are actually found are compensated, making the model efficient and cost-effective.
- Constructive collaboration with security researchers: This fosters a positive and productive environment for both parties.
- Learning effect for developers and internal security personnel: The knowledge gained from the vulnerabilities found can be used directly in the training and further development of internal teams.
As a bank, Raiffeisen has a profound responsibility to protect its customers and their data securely. In a digitally networked world, Raiffeisen must use all available tools to fulfill this responsibility. Bug bounty programs are simply part of ensuring the highest level of security and constantly strengthening customer trust.
First-hand insights into ethical hacking
To make the three-dimensional picture complete, Mauro Mattia Sbicego brought in the perspective of ethical hacking. An ethical hacker and student, Mauro has been active in the bug bounty scene for five years. His passion for security has led him to ETH Lausanne, where he will further specialize in the topic starting in the fall. He appreciates the depth that bug bounty programs offer - compared to traditional testing, hackers like him can dive in more intensively and under real-world conditions. That depth is evident in the different types of attacks he deals with, from SQL injections to command injections to buffer overflows.
For Mauro, it's not just the financial incentive that makes bug hunting attractive. The opportunity to constantly explore new systems, devices and techniques, and the freedom to do so without time pressure, is invaluable to him. But collaboration is even more important: A good relationship with the client and clear communication channels, for example through specialized hacking dashboards, are crucial.
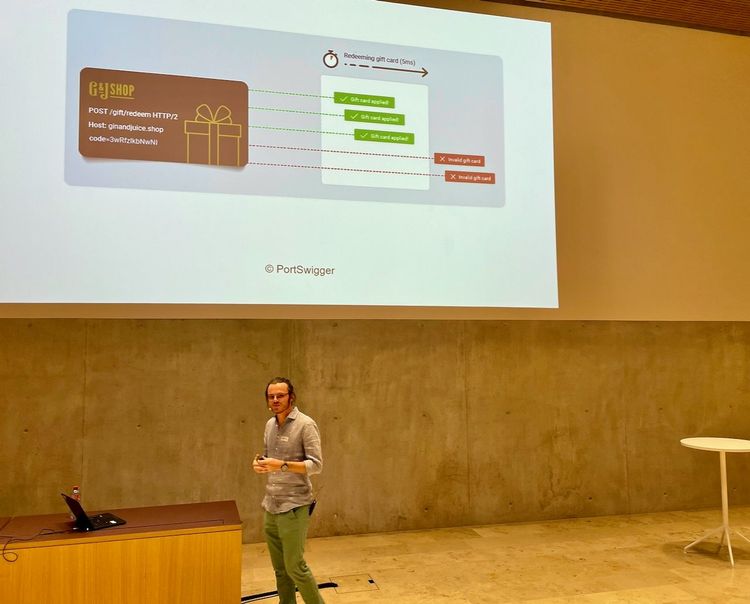
Live hack miracle: making money grow through race conditions
In an impressive demonstration, Mauro showed a "live hack" in which he used "race conditions" to trick an eShop. The principle behind it: He was faster than the system and entered commands or codes before the system could register that a value had already been used - and this not in seconds, but in milliseconds. Using this approach, he managed to multiply money virtually "out of thin air," for example by achieving exponential growth with a voucher and using it to buy more vouchers. The problem: such vulnerabilities are difficult to detect, are rarely tested, and are difficult to fix. Sometimes it might even be necessary to rebuild the entire architecture. As Mauro aptly noted, "As long as you don't know exactly how it works, you can't fix it successfully." Because only with this understanding can such gaps be effectively closed.
Holistic security
In the panel discussion that followed, the three speakers agreed: Security must be viewed holistically. It is not enough just to know about vulnerabilities - it is crucial that knowledge of these vulnerabilities is available where they can be remedied. Even the most thorough testing covers only a fraction of the possible attack vectors. And even after a vulnerability is discovered, the work doesn't end. It's about fixing it correctly and integrating the lessons learned into the development process. For companies like Raiffeisen, this is a top priority, because the responsibility to their customers is enormous.

The presentations met with great interest and there were numerous questions to the speakers. It was obvious that the topic had struck a nerve and triggered profound discussions and exchanges of ideas. These lively discussions then continued in bright sunshine during the aperitif. It was an excellent opportunity to network and deepen the discussions in a relaxed environment.